1
What is a component of a routing table entry?
2
Refer to the exhibit. The network in the exhibit is fully operational. What two statements correctly describe the routing for the topology that is shown? (Choose two.)
3
What is the purpose of a default gateway?
4
Refer to the exhibit. All devices shown in the exhibit have factory default settings. How many broadcast domains are represented in the topology that is shown?
5
Which intermediary devices could be used to implement security between networks? (Choose two.)
6
What are three common problems with a large network? (Choose three.)
7
Refer to the exhibit. Using the network in the exhibit, what would be the default gateway address for host A in the 192.133.219.0 network?
8
Refer to the exhibit. A network administrator notices that there are too many broadcasts on the network. What two steps can the network administrator take to resolve this problem? (Choose two.)
9
What two characteristics are commonly associated with dynamic routing protocols? (Choose two.)
10
In an IPv4 environment, what information is used by the router to forward data packets from one interface of a router to another?
11
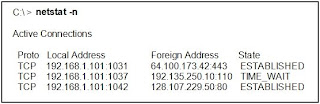
Refer to the exhibit. A network administrator is troubleshooting a connectivity problem and needs to determine the address that is used to forward network packets out the network. Using the netstat -r command, the administrator would identify which address as the address to which all hosts send packets that are destined for an outside network?
12
Which portion of the network layer address does a router use to forward packets?
13
What information is added during encapsulation at OSI Layer 3?
14
Which three statements are true about routes and their use? (Choose three.)
15
What statement describes the purpose of a default route?
16
When the destination network is not listed in the routing table of a Cisco router, what are two possible actions that the router might take? (Choose two.)
17
In a connectionless system, which of the following is correct?
18
If the default gateway is configured incorrectly on the host, what is the impact on communications?
19
What are the key factors to consider when grouping hosts into a common network? (Choose three.)
20
Which IP packet field will prevent endless loops?
21
What type of routing uses information that is manually entered into the routing table?
What is a component of a routing table entry?
- the next-hop address
2
Refer to the exhibit. The network in the exhibit is fully operational. What two statements correctly describe the routing for the topology that is shown? (Choose two.)
- 192.168.0.2 is the next-hop address that is used by R3 to route a packet from the 10.0.0.0 network to the 172.16.0.0 network.
- 192.168.0.1 is the next-hop address that is used by R2 to route a packet from the 172.16.0.0 network to the 192.168.12.0 network.
3
What is the purpose of a default gateway?
- identifies the device that allows local network computers to communicate with devices on other networks
4
Refer to the exhibit. All devices shown in the exhibit have factory default settings. How many broadcast domains are represented in the topology that is shown?
- 4
5
Which intermediary devices could be used to implement security between networks? (Choose two.)
- router
- firewall
6
What are three common problems with a large network? (Choose three.)
- performance degradation
- security issues
- host identification
7
Refer to the exhibit. Using the network in the exhibit, what would be the default gateway address for host A in the 192.133.219.0 network?
- 192.133.219.1
8
Refer to the exhibit. A network administrator notices that there are too many broadcasts on the network. What two steps can the network administrator take to resolve this problem? (Choose two.)
- Replace S2 with a router.
- Subnet the 192.168.0.0 /24 network.
9
What two characteristics are commonly associated with dynamic routing protocols? (Choose two.)
- provide routers with up-to-date routing tables
- consume bandwidth to exchange route information
10
In an IPv4 environment, what information is used by the router to forward data packets from one interface of a router to another?
- destination network address
11
Refer to the exhibit. A network administrator is troubleshooting a connectivity problem and needs to determine the address that is used to forward network packets out the network. Using the netstat -r command, the administrator would identify which address as the address to which all hosts send packets that are destined for an outside network?
- 10.10.10.6
12
Which portion of the network layer address does a router use to forward packets?
- network portion
13
What information is added during encapsulation at OSI Layer 3?
- source and destination IP address
14
Which three statements are true about routes and their use? (Choose three.)
- If the destination network is directly connected, the router forwards the packet to the destination host.
- If no route exists for the destination network and a default route is present, the packet is forwarded to the next-hop router.
- If the originating host has a default gateway configured, the packet for a remote network can be forwarded using that route.
15
What statement describes the purpose of a default route?
- A host uses a default route to transfer data to a host outside the local network when no other route to the destination exists.
16
When the destination network is not listed in the routing table of a Cisco router, what are two possible actions that the router might take? (Choose two.)
- The router discards the packet.
- The router forwards the packet out the interface indicated by the default route entry.
17
In a connectionless system, which of the following is correct?
- The destination is not contacted before a packet is sent.
18
If the default gateway is configured incorrectly on the host, what is the impact on communications?
- The host can communicate with other hosts on the local network, but is unable to communicate with hosts on remote networks.
19
What are the key factors to consider when grouping hosts into a common network? (Choose three.)
- purpose
- geographic location
- ownership
20
Which IP packet field will prevent endless loops?
- time-to-live
21
What type of routing uses information that is manually entered into the routing table?
- static







 4:28:00 PM
4:28:00 PM
 DPY
DPY